Denial-of-service (DoS) and distributed denial-of-service (DDoS) attacks
A Distributed Denial of Service (DDoS) Assault is one of the most powerful weapons on the Internet. If a website getting "brought down by hackers," it generally means that it has become a target of a DDoS attack. In brief, this implies that criminals have tried to make a server or device inaccessible by overwhelming or collapsing a website with too much traffic. According to Weisman from NortonLife Lock, Distributed Denial of Service attacks hit websites and online services. The aim is to flood them with more data than the server or the network can handle. The goal is to make the website or service inoperable.
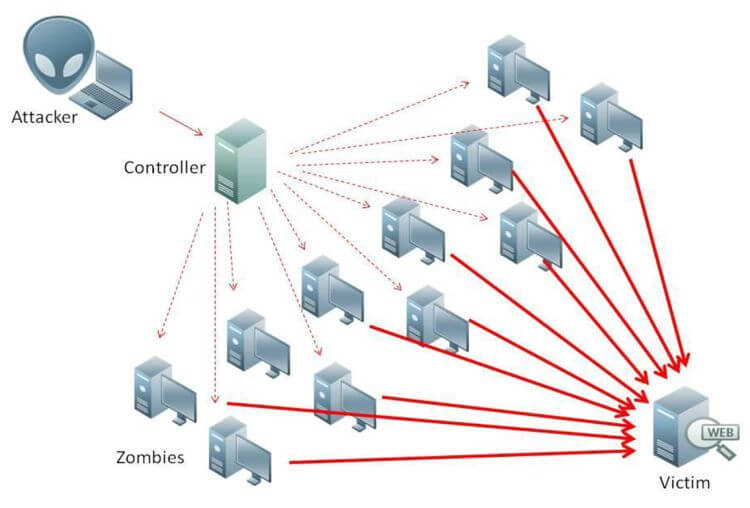
Fig. DDoS Attack
When starting the DDoS Attack?
In 2000, Michael Calce, a 15-year-old boy who used the online name "Mafiaboy," conducted one of the first DDoS attacks reported. Calce also broken into a variety of schools ' computer networks. They used their database to conduct a DDoS assault that disrupted many major websites, including CNN, E-Trade, eBay, and Yahoo. Calce was tried at the Quebec Youth Court for his crimes. As an adult, he became a "white-hat intruder" who discovered flaws in big corporations ' computer systems (Weisman, n.d.)
The most recently DDoS attack took place in October 2016, a flood of distributed denial of service (DDoS) attacks affecting tens of millions of Internet Protocol (IP) addresses was detected and the Dyn domain name network (DNS) was targeted. This attack has a magnitude of 1.2 Terabytes and implicated the Internet of Things (IoT).
According to the 12th annual report of the Arbor Network released in Waterman2, the scale and rise of the DDoS attacks have been the greatest in the last year and have also grown in magnitude over the last few years.
The targets at this kind of attack have a range from own home to the biggest organizations such as the government. Arbore network has shown that are around 1000 DDoS attack every day (Mahjabin et. al., 2017).
One of the reasons for these attacks is related to the desire to steal money. One of the main motivations to assault such users is for some financial gain, but the enticing goal for a DDoS attack can be porn or online gambling sites (Mahjabin et. al., 2017).
In a quarterly survey by Kaspersky Lab, it can be found that several e-commerce pages were the primary focus of DDoS attacks in the second quarter of 2011( KasperskyLab, 2011 cited in Mahjabin et. al. 2017)
In 2000, Michael Calce, a 15-year-old boy who used the online name "Mafiaboy," conducted one of the first DDoS attacks reported. Calce also broken into a variety of schools ' computer networks. They used their database to conduct a DDoS assault that disrupted many major websites, including CNN, E-Trade, eBay, and Yahoo. Calce was tried at the Quebec Youth Court for his crimes. As an adult, he became a "white-hat intruder" who discovered flaws in big corporations ' computer systems (Weisman, n.d.)
The most recently DDoS attack took place in October 2016, a flood of distributed denial of service (DDoS) attacks affecting tens of millions of Internet Protocol (IP) addresses was detected and the Dyn domain name network (DNS) was targeted. This attack has a magnitude of 1.2 Terabytes and implicated the Internet of Things (IoT).
According to the 12th annual report of the Arbor Network released in Waterman2, the scale and rise of the DDoS attacks have been the greatest in the last year and have also grown in magnitude over the last few years.
The targets at this kind of attack have a range from own home to the biggest organizations such as the government. Arbore network has shown that are around 1000 DDoS attack every day (Mahjabin et. al., 2017).
One of the reasons for these attacks is related to the desire to steal money. One of the main motivations to assault such users is for some financial gain, but the enticing goal for a DDoS attack can be porn or online gambling sites (Mahjabin et. al., 2017).
In a quarterly survey by Kaspersky Lab, it can be found that several e-commerce pages were the primary focus of DDoS attacks in the second quarter of 2011( KasperskyLab, 2011 cited in Mahjabin et. al. 2017)

Figure 2. Breakdown of attacked sites in Q2 2011.
The most common reasons for this attack are (Mahjabin et. al., 2017):
- Financial or economic benefits, attacks who come under this motive are known to be the riskiest attacks because they expect a financial benefit from the attacks. In such a scenario, the assailants are highly experienced technicians. Therefore, in the present case, this type of attack is hard to stop.
- Revenge, this is another reason for the DDoS assaults, where some disgruntled (possibly technologically less skilled) individuals carry out the attacks as a compensation of some alleged oppressions.
- Ideological belief, some of the attackers were inspired to strike the goal because of their ideological beliefs. This has become an important factor behind the assaults on DDoS. Although they are not as common as other reasons, their impacts and scales are as high as they have been seen in recent years.
- Intellectual challenge, the attackers of this group are mainly motivated to conduct DDoS attacks to show off their capabilities and power. The availability of the easy-to-use attack tools and botnets motivates these attackers to conduct experiments of DDoS attacks.
- Cyberwarfare, this is another essential incentive for an assault that poses a threat and has a significant economic effect on its goals. Typically, some well-trained people from a military or terrorist organization are carrying out attacks of this kind.
DDoS components
1) Master Mind/Planner: The Original Attacker, who creates reasons and answers for, why, when, how and by whom the attack will be performed.
2) Controller/Handler: Co-ordinator of the original attacker, who may be one or more than one machine, is used to exploit other machines to process DDoS attack
3) Agents/Zombies/Botnets: Agents, also known as slaves or attack daemons, subordinates are programs that actually conduct the attack on the victim. These programs are usually deployed on host computers. These daemons influence both the machines: target and the host computers. It facilitates the attacker to gain access and infiltrate the host computers.
4) Victim/Target: A victim is a target host that has been selected to receive the impact of the attack.
To sum up, the DDoS attack is one of the most destructive cyber attacks due to a large number of devices involved and the purpose of which that was created. Over the years these attacks have produced important material damage and also the loss of vital information. Many attacks start via a phishing email, malware or and other mass infection techniques. Companies should improve and work in their security on a regular base.
How it takes place?
Typically, DDoS attackers rely on botnets – collections of a network of malware-infected systems that are centrally controlled. These infected endpoints are usually computers and servers but are increasingly IoT and mobile devices. The attackers will harvest these systems by identifying vulnerable systems that they can infect through phishing attacks, malvertising attacks, and other mass infection techniques.
DDoS impact
Cash, resources, clients and even credibility may be lost in the event of a DDoS attack. Depending on the severity of the assault, services may be down for 24 hours, several days, or even a week. In reality, Kaspersky Lab's survey revealed that one in five DDoS attacks could last for days or even weeks, attesting to their complexity and serious threat to all businesses.Defense
A modern DDoS defense should include four critical requirements:
- Precision: It’s crucial for companies to implement a precise DDoS defense system
- Scalability: Given the sheer size of today’s DDoS attacks it’s more important than ever for DDoS protection systems to be scalable in depth, breadth and height.
- Wartime Response Efficiency:An automated DDoS defense system can eliminate the need for costly and time-consuming manual intervention.
- Affordability: Companies can keep costs low without sacrificing performance with smaller, more efficient and more affordable DDoS protection system. This reduces the number of appliances needed, decreases cost and cuts down on rack space, saving both time and money.
To sum up, the DDoS attack is one of the most destructive cyber attacks due to a large number of devices involved and the purpose of which that was created. Over the years these attacks have produced important material damage and also the loss of vital information. Many attacks start via a phishing email, malware or and other mass infection techniques. Companies should improve and work in their security on a regular base.
References list:
KnowHostBlog, 2019. DDoS Attack. [image] Available at: <https://www.google.com/url?sa=i&url=https%3A%2F%2Fwww.knownhost.com%2Fblog%2Fddos-protection-critical%2F&psig=AOvVaw2_4fpFrSXfFVQRAlbp7y4E&ust=1583832896322000&source=images&cd=vfe&ved=0CAIQjRxqFwoTCPjZj8WLjegCFQAAAAAdAAAAABAD> [Accessed 9 February 2020]
Mahjabin, T., Xiao, Y., Sun, G. and Jiang, W., 2017. ‘A survey of distributed denial-of-service attack, prevention, and mitigation techniques’, International Journal of Distributed Sensor Networks. [Online]. Availble at doi: 10.1177/1550147717741463. [Accessed 9 February 2020]
Weisman, S., n.d. What Is A Ddos Attack?. [online] Us.norton.com. Available at: <https://us.norton.com/internetsecurity-emerging-threats-what-is-a-ddos-attack-30sectech-by-norton.html> [Accessed 8 February 2020].
Mahjabin, T., Xiao, Y., Sun, G. and Jiang, W., 2017. ‘A survey of distributed denial-of-service attack, prevention, and mitigation techniques’, International Journal of Distributed Sensor Networks. [Online]. Availble at doi: 10.1177/1550147717741463. [Accessed 9 February 2020]
Weisman, S., n.d. What Is A Ddos Attack?. [online] Us.norton.com. Available at: <https://us.norton.com/internetsecurity-emerging-threats-what-is-a-ddos-attack-30sectech-by-norton.html> [Accessed 8 February 2020].
So what is the impact of DoS attacks? You could find evidence to back up any statement you think might be true, this would give more of your own commentary and show cross referencing techniques.
ReplyDelete